As discussed previously, MIMO is a method for increasing effective throughput by deliberately exploiting multipath propagation. The different generations of WiFi make use of this in varying ways.
802.11n (Wi-Fi-4)
This supported the more limited Single User MIMO (SU-MIMO). As its name suggests, SU-MIMO means the access point can only be sent to one client at a time.
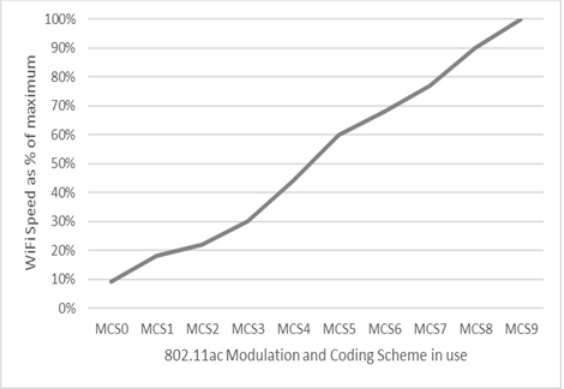
802.11ac (Wi-Fi-5)
This added MU-MIMO (d). The (d) stands for downlink. With MU-MIMO (d), only one station can transmit, but multiple stations can receive at any given time.
802.11ax (Wi-Fi-6)
This was extended to MU-MIMO (u/d). Now, multiple devices can both transmit and receive simultaneously.
MU-OFDMA
Basic OFDM has been supported since 802.11a (Wi-Fi-2). 802.11ax (Wi-Fi-6) has extended this to now support multiple users.
You could think of the older style of OFDM as a sequence of trucks, each delivering boxes from one vendor at a set time every day. MU-OFDMA allows each truck to be loaded with multiple vendor’s boxes. It also allows the delivery schedule of those trucks to happen only when there’s a full load.
Older Wi-Fi specifications were designed for web browsing and checking email. Congestion emerged as video streaming, AR/VR, and gaming became common. This, combined with more and more client devices transmitting at the same time, meant that the queuing caused by simple OFDM increased latency.
Perhaps most importantly, MU-OFDMA allows priorities to be set not only per client but per protocol/traffic type. In other words, the access point could prioritize video streaming at one level, IoT messages at another, and mission-critical VOIP at the highest.
802.11p (DSRC)
An amendment to the broader IEEE 802.11 Wireless LAN (WLAN) standard, 802.11p is tailored for high-speed, short-range communication in a vehicular environment. The standard operates in the 5.9 GHz frequency band and utilizes the Dedicated Short-Range Communications (DSRC) protocol to ensure low latency and reliable data exchange.
The primary advantage of DSRC over 4G/LTE or 5G for V2X is that it can provide some value in the absence of any infrastructure. If two V2X-equipped cars come within range of each other, they will exchange information in a peer-to-peer fashion. This would function even in the middle of the Sahara.
In 2016, Toyota became the first automaker to introduce cars equipped with V2X systems, followed by GM in 2017. Both of these used DSRC as opposed to 4G/LTE or 5G. While DSRC was the first standard the automotive industry adopted, that is changing for several reasons. Compared to 4G/LTE or 5G for V2X, DSRC suffers from the following limitations:
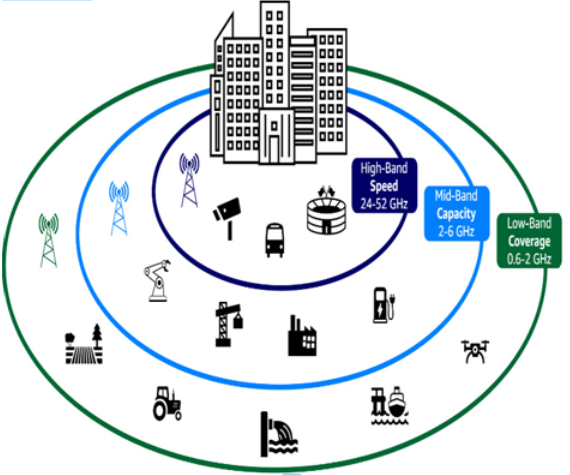
Limited capacity and scalability: DSRC operates in a narrow frequency band (5.9GHz), which limits its capacity to support a high number of simultaneous connections in dense traffic scenarios. 5G offers broader bandwidth and improved spectral efficiency, allowing it to handle more devices and users concurrently.
Lower data rates: DSRC offers lower data rates compared to 5G, which hinders its ability to support advanced V2X applications that require higher throughput, such as high-definition video streaming for autonomous vehicles. 5G, with its enhanced data rates, can better accommodate these demanding use cases.
Latency: Although DSRC provides relatively low latency communication, 5G has the potential to achieve even lower latencies, especially with the implementation of 5G Ultra-Reliable Low-Latency Communication (URLLC). URLLC can enable mission-critical applications and real-time control systems that demand near-instantaneous response times.
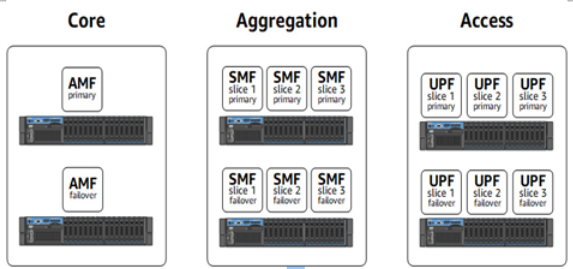
Network slicing: 5G supports network slicing, a feature that allows the creation of virtual networks tailored to specific use cases or applications. This enables the allocation of dedicated resources for V2X communications, ensuring the desired performance levels. DSRC, on the other hand, does not offer this level of customization and flexibility.
Global harmonization: While DSRC has been adopted in some regions, it has not achieved global harmonization, leading to inconsistencies in spectrum allocation and regulation across different countries. 5G has a more unified approach, with global standardization and broader adoption, making it more attractive for V2X implementations across various regions.
Keeping all of this in mind, automakers have begun to include both in their chipsets. The idea is that cellular networks are the primary communication path, and when those are not available, the chipset will leverage DSRC for peer-to-peer vehicle communication when and where it can.
More Details