Oct 8, 2022
Spatial streams – Understanding Network and Security for Far-Edge Computing
The term for beamforming as it is implemented within Wi-Fi is spatial streams.
While some vendors of 802.11n (Wi-Fi-4) devices did implement beamforming, it was through proprietary mechanisms that were specific to each product line. 802.11ac (Wi-Fi-5) was the first to include it as part of the specification.
When a Wi-Fi access point has beamforming enabled, it first estimates the angle of arrival of each client by comparing small differences in arrival times of a signal across multiple antennas that are close together. Once it knows the direction in which it needs to steer the beam, it will have those antennas broadcast the signal at slightly different times. The pattern that’s used is known as a steering matrix.
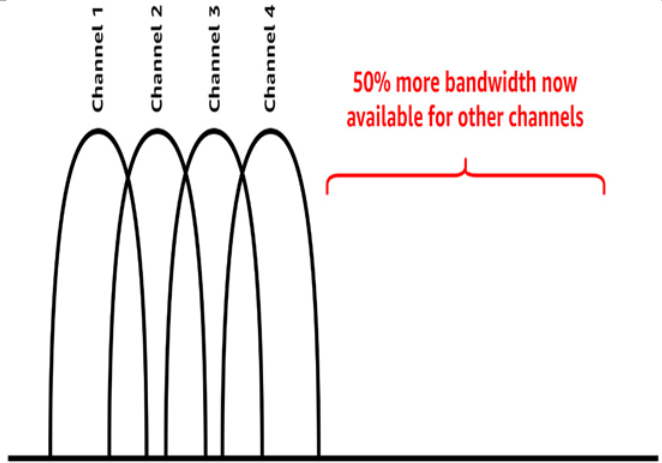
This deliberately introduces interference because the waves now overlap a little bit. However, not all interference is the same. Some are constructive interference, which makes the signal stronger in one direction, while destructive interference makes it weaker in another:
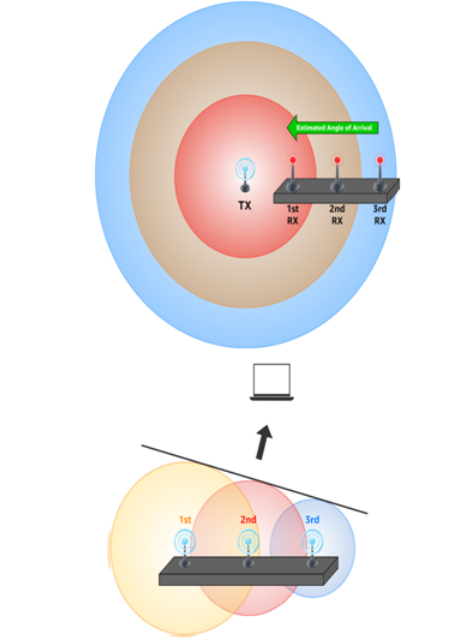
Figure 3.32 – Beamforming with 802.11ac (Wi-Fi-5)
The net effect of all this is to maximize the signal strength on a per-client basis. This means the signal effectively travels farther and penetrates obstacles better. With older Wi-Fi specifications, all you could do is increase the power output of an omnidirectional signal or add Wi-Fi repeaters.
This is one of the reasons for a seemingly endless multiplication of antennas on even consumer-grade access points. More antennas on both the AP and the clients are better for Wi-Fi throughput – up to a point13. Regardless of the number of antennas, the 802.11ac (Wi-Fi-5) specification supports a maximum of four spatial streams to be active at once.
13 Two antennas are the minimum for beamforming to function at all, while three is recommended.
802.11ax (Wi-Fi-6) increased this to eight and also enhanced it by including client-side modifications that help the AP figure out where a given client is instead of leaving all the work on the AP.
More Details